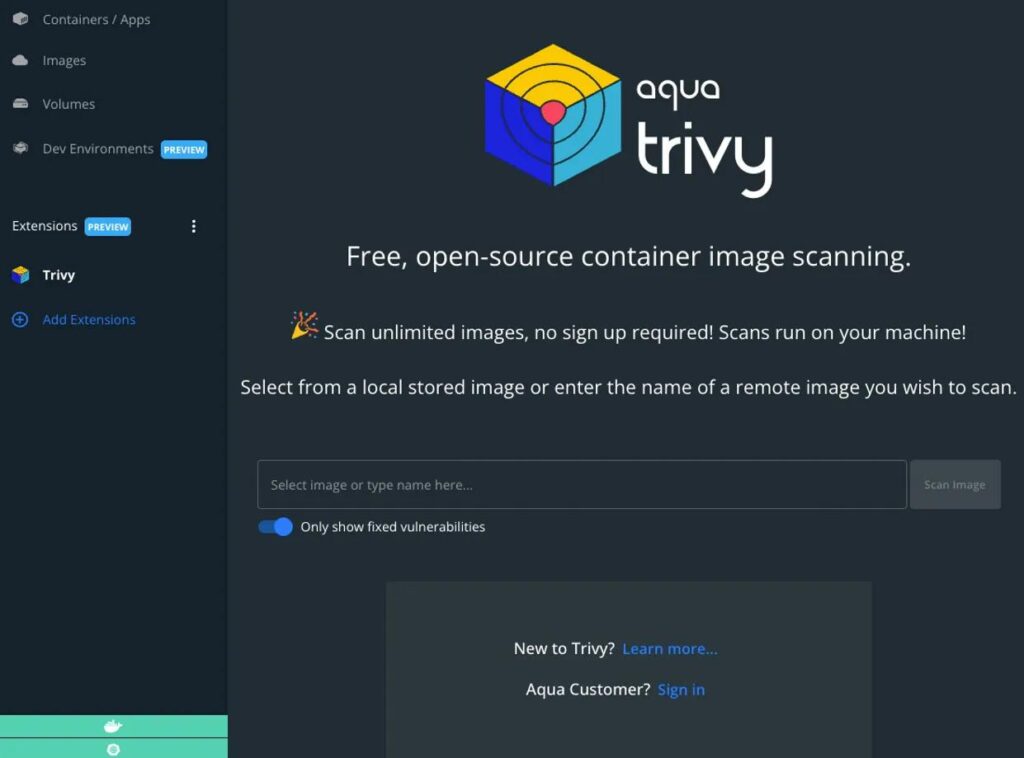
Modern DevSecOps practices rely heavily on automation to secure applications before they reach production. Organizations integrate vulnerability scanners into their pipelines to detect risks early, enforce compliance, and maintain visibility across their infrastructure. One of the most widely adopted tools in this space is Trivy, an open-source scanner designed to identify vulnerabilities in containers, filesystems, and infrastructure configurations.
Because Trivy is trusted to protect systems, it often operates with deep access to sensitive environments.
That trust, however, creates a new kind of risk.
When a security tool becomes part of the attack surface, the consequences are far more severe than a traditional vulnerability. Instead of exploiting weaknesses in applications, attackers can compromise the very mechanism designed to detect those weaknesses.
What Happened in the Trivy Supply Chain Attack Scenario?
The Trivy supply chain attack is best understood as a high-impact threat scenario rather than a single confirmed breach. It represents a class of attacks where adversaries target security tools themselves by manipulating their distribution, update mechanisms, or execution environments.
In such a scenario, attackers may attempt to tamper with Trivy’s binaries, compromise its vulnerability database, or inject malicious logic into the update process. Since Trivy frequently fetches updates to stay current with newly discovered vulnerabilities, this update channel becomes a critical point of trust. If compromised, it can be used to deliver malicious payloads directly into secure environments.
What makes this particularly dangerous is the context in which Trivy operates. It is often integrated into CI/CD pipelines, where it runs automatically with access to source code, container images, and sometimes even secrets. If an attacker gains control over the tool or its data sources, they can manipulate scan results, hide real vulnerabilities, or introduce malicious behavior into the pipeline itself.
Who is Affected?
The potential impact of a Trivy supply chain attack extends across a wide range of environments. Organizations that rely on containerized applications, cloud-native architectures, or automated deployment pipelines are particularly exposed. This includes DevSecOps teams, Kubernetes-based infrastructures, and enterprises that integrate security scanning into their development workflows.
The risk becomes significantly higher in environments where Trivy is granted elevated permissions or where its outputs are used as a gatekeeper for deployment decisions. In such cases, a compromised scanner can influence critical processes, allowing insecure or malicious code to pass through undetected.
Ultimately, any organization that places implicit trust in automated security tools without verification becomes part of the affected landscape.
Why This Attack Matters
The importance of this scenario lies in how it challenges a fundamental assumption in cybersecurity: that security tools can be trusted by default. In reality, these tools are software components like any other, and they can be targeted, manipulated, or compromised.
When a vulnerability scanner like Trivy is compromised, the impact is not immediately visible. Instead of causing system failures or triggering alerts, it creates a false sense of security. Organizations may continue deploying applications under the belief that they are safe, while hidden vulnerabilities remain undetected.
This makes the attack particularly dangerous. It does not break the system — it quietly undermines the mechanisms designed to protect it.
What Makes Security Tool Attacks Unique?
Attacks on security tools differ from traditional attacks because they operate within trusted environments. Tools like Trivy are executed as part of routine processes, often with high privileges and minimal scrutiny. Their outputs are rarely questioned, and their behavior is assumed to be reliable.
This level of trust allows attackers to operate indirectly. Instead of targeting the application, they influence the tool that evaluates the application. By doing so, they can bypass security controls without triggering conventional defenses.
Another unique aspect is the scale of impact. A single compromised tool can affect multiple projects, repositories, and environments simultaneously, making it a powerful entry point for large-scale attacks.
Core Security Concerns
One of the primary concerns in a Trivy-related attack is the integrity of scan results. If attackers can manipulate vulnerability data or scanning logic, they can hide critical issues or generate misleading reports. This undermines the entire purpose of the tool and can lead to insecure deployments.
Another concern is the exposure of sensitive data during scanning. Since Trivy analyzes containers and filesystems, it may encounter credentials, configuration files, and secrets. If the tool is compromised, this information can be extracted and transmitted without detection.
There is also the issue of over-reliance on automation. Many organizations use Trivy as a gatekeeper in their pipelines, allowing deployments only if scans pass. If the tool itself is compromised, this control mechanism becomes ineffective, allowing malicious or vulnerable code to enter production environments.
How to Prevent Supply Chain Risks in Trivy
Mitigating these risks requires a shift from blind trust to continuous verification. Organizations must ensure that Trivy is installed from trusted sources and that its binaries are validated using checksums or digital signatures. Update mechanisms should be secured, and any changes to vulnerability databases should be monitored for anomalies.
It is also essential to limit the permissions granted to the tool. Running Trivy with the principle of least privilege reduces the potential impact of a compromise. Isolating scanning environments and avoiding unnecessary access to sensitive systems can further minimize risk.
CI/CD pipelines should be secured with strict access controls and continuous monitoring. Any unusual behavior, such as unexpected scan results or changes in tool performance, should be investigated promptly. Additionally, relying on multiple security tools for validation can help detect inconsistencies and reduce dependence on a single point of trust.
Final Thoughts
The Trivy supply chain attack scenario highlights a critical evolution in cybersecurity threats. Attackers are no longer focused solely on applications; they are targeting the tools and processes that organizations depend on for security.
This shift requires a new mindset.
Security tools must be treated as part of the attack surface, not as unquestionable safeguards. Every component in the pipeline, including scanners, build systems, and update mechanisms, must be continuously validated and monitored.
For developers and DevOps teams, this means implementing stronger controls around tool usage and integration. For security professionals, it emphasizes the need for layered defenses and independent verification mechanisms.